In marketing, it’s common practice for companies to make bold claims about their product. Such claims are known to influence customers’ behavior and as a result, increase sales. The VPN industry is no stranger to this marketing practice.

- Unconditional 30-day money-back guarantee
- No activity logs and no connection logs
- Easy-to-use apps for all devices
Case in point, nearly all VPN providers use the phrase ‘no logs policy’ prominently on their landing pages. It would be nice if providers kept the end of their bargain. But, it is technically impossible for them to refrain from logging users’ data.
In a fair world, ‘no-logs’ logically means that the provider doesn’t record any data whatsoever. If VPNs were to strictly adhere to this policy, resolving customer queries and managing the service would be hard without any data logging. Most VPN services tend to ignore these nuances, and as such, their zero logs policy is rarely accurate.
That said, recording users’ data isn’t entirely wrong, especially if it helps improve service delivery. The problem arises when VPN companies store sensitive data such as IP addresses, websites visited, and files downloaded. You want to avoid VPNs that keep these types of data.
Therefore, before signing up for a VPN service, take time to know precisely which kind of information they record and for what purpose.
An excellent place to seek this information is on a provider’s FAQ section as well as the Privacy Policy, and the Terms and Conditions agreement. To make it easier for you, we evaluated a couple of VPNs to ascertain their zero logs policy.
Here’s the Best No log VPNs
After a thorough investigation of various providers’ logging policies, we recommend the following VPNs. Although some may record an insignificant amount of users’ data, they only store non-personal identifiable information.
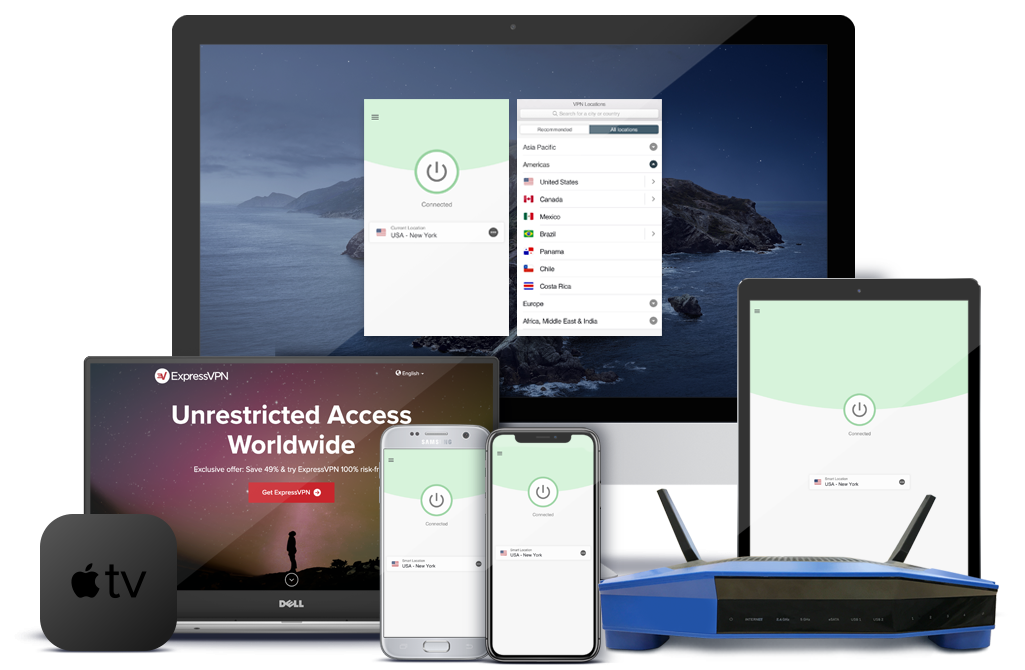
- ExpressVPN: This provider is based in the British Virgin Islands, where there are no data retention laws. Accepts cryptocurrencies, including Bitcoin. The provider also scores high in connection speeds and server coverage.
- NordVPN: Has a transparent privacy policy that confirms their no logs policy. The service provides double encryption, offering extra privacy protection against monitoring. Accepts anonymous payment using either Ripple, Ethereum, or Bitcoin.
- Cyber Ghost: CyberGhost is based in Romania, a VPN-friendly country that respects online privacy. The VPN provider doesn’t log any of your personal activities. The provider owns and manages its on-site servers; thus, users’ data is free from third-party intrusion.
- IPVanish: In addition to its affordability, IPVanish offers a relatively reliable private connection. While the company is based in the U.S., it boasts adherence to a strict no-logs policy.
- PrivateVPN: Although it has a small server network, all its infrastructure is in-house managed, eliminating the risk of third-party interference. Plus, it hosts a number of advanced features for maximum privacy protection.
Criteria Used in Evaluating No Log VPNs
Of course, you must check a VPN’s privacy policy to determine whether they log any data. By checking, we don’t just mean skimming through the policy; rather, you have to read the fine print of the policy. And more.
It’s not uncommon to find a VPN with contradicting statements about logging. On their landing page, a provider may claim that they don’t record any data. Only for them to confess later in the logging policy they indeed keep sensitive logs such as device type and timestamps.
In addition to reviewing the providers’ privacy policy page, we also considered the following factors, influencing a VPN’s privacy protection:
- Jurisdiction
- Anonymous payment options
- Encryption standards
- Security features
1. ExpressVPN
As mentioned earlier, ExpressVPN operates in a VPN-friendly country; the British Virgin Islands. As such, the company is under no pressure from the government to keep an account of the user’s activities.
Additionally, the VPN has a consistent privacy policy that agrees with their ‘no logs’ claim. The only data they record are login dates, server location, and amount of data transferred, which is used to offer customer support solutions.
While it’s difficult to take their word for it, the recent legal clash between the provider and the Turkish authorities, verified ExpressVPN’s no logs policy.
The authorities were trying to find incriminating evidence for an investigation involving the assassination of a Russian ambassador. Unfortunately, they were unable to find any actionable data on the VPN’s servers used by the suspect.
Also, ExpressVPN upgraded its infrastructure technology by incorporating RAM-mode disk in its servers. This technology, also known as ‘TrustedServer,’ ensures that no data is stored on the servers. Connections to these servers are encrypted using 256-bit keys over the OpenVPN default protocol alongside HMAC authentication.
When signing up for ExpressVPN, you are allowed to use a burner or disposable email address to keep your true identity under wraps. In the same vein, the provider accepts Bitcoin payments.
Users’ privacy is further enhanced by the built-in WebRTC, DNS, and IPv6 leak protection. Other security features include split tunneling and kill switch abilities.
Pros
- Transparent no logs policy
- Strong encryption standards and leak protection
- Accepts Bitcoin as payment
- Fast connection speeds
Cons
- Not as affordable as some VPN services
2. NordVPN
NordVPN is one of the few VPNs that have a complete zero logs policy. A claim that has been put to the test by an independent auditor, who eventually concluded that the provider doesn’t log any traffic.
Moreover, those who don’t want to leave any paper trail can pay for the service using the accepted cryptocurrencies.
The provider’s security suite includes AES 256-bit keys over the OpenVPN protocol, with SHA384 authentication and perfect forward secrecy tool. This tool generates a unique session periodically such that, if one of the session keys is compromised, data from the previous and subsequent sessions won’t be affected. The VPN also has a kill-switch feature, meant to maintain your privacy, in case your connection drops.
For guaranteed security, NordVPN transmits user’s data through two encrypted tunnels. As such, even if your data is compromised, hackers can’t decipher much out of it. This double encryption feature works perfectly for users in countries such as China and Iran, where there are stringent internet censorship laws.
On top of it all, the VPN is based in Panama, where there are no mandatory data retention laws. This makes NordVPN ideal for torrenting and unblocking geo-restricted content.
Also, the VPN provider boasts extensive server coverage, amounting to over 5,000 servers in more than 60 countries.
Pros
- Lots of extra security features
- Comprehensive server coverage
- Proven zero-logging policy
- Allows P2P file sharing
- Accepts a wider range of cryptocurrency payments
Cons
- Lacks split tunneling feature
3. CyberGhost
CyberGhost is a Romania-based VPN with a strong focus on privacy. This is evident from its no traffic and connection logs that are complemented by its privacy-friendly jurisdiction. The company even goes ahead to release annual transparency reports in a bid to win users’ trust.
Similar to other competitors, CyberGhost utilizes the advanced 256-bit keys encryption, alongside SHA256 authentication as well as perfect forwarding secrecy.
The VPN also has an automatic kill switch feature on all its client apps in addition to DNS, IPv6, and WebRTC leak protection abilities.
Unlike most VPNs in the market, CyberGhost gives you the freedom to set up automatic protection on untrustworthy networks. So, the VPN will launch a connection every time you are using a public WI-FI or a blacklisted network.
When registering for the VPN service, the provider allows you to use a made-up user name instead of your real name. The company then assigns you a serial number for activating your account. As such, the little information collected it collects is not tied to an individual, and it’s used to track servers’ performance.
The only red flag we noticed is that CyberGhost records daily log-ins and sums up them up for a month before deleting them. Such an extended period can be leveraged by hackers or other third parties to extract valuable data. Nonetheless, the VPN is pretty easy to use and has relatively fast connection speeds.
Pros
- Easy to use
- Competitive connection speeds
- Accepts Bitcoin payments
- Has optimized servers for torrent downloads
Cons
- Has a questionable privacy policy
4. IPVanish
Judging from its base of operation (the US), IPVanish doesn’t seem like the go-to privacy VPN. Worse still, the company that previously owned the VPN once provided data evidence to help in a criminal investigation.
While we appreciate their cooperation with the authorities to bring down criminals, users’ trust was betrayed. Fast forward, today, IPVanish is owned by a different company. Although the service’s jurisdiction wasn’t changed, the new owners never fail to assure users that no data is recorded.
So, IPVanish wouldn’t materialize any data evidence if it were required to do so again. The VPN’s jurisdiction doesn’t have to cause chill since the US has no mandatory data retention laws. Nonetheless, the US government is known to coerce tech companies to hand over customers’ encryption keys.
One of the biggest perks of relying on IPVanish privacy protection is that the provider owns and maintains its global network of physical servers. This gives the company complete control over users’ data, ensuring third-parties do not interfere.
IPVanish used to accept Bitcoin payments in its early years, but the service no longer supports this payment option. However, the VPN is compatible with TOR browser; for those who want to beef up their online privacy.
The service also uses 256-bit key encryption on all its protocols in addition to the ‘scramble obfuscation’ feature that hides users’ traffic.
Pros
- Compatible with Tor browser
- No IP leaks or malware found
- Owns and operates all the servers on their networks
- Reliable connection speeds
Cons
- Doesn’t accept Bitcoin
5. PrivateVPN
PrivateVPN is based in Sweden, which is a member of the 14-Eyes Alliance. Moreover, Sweden itself has mandatory data retention law though it only applies to communication services such as ISPs and mobile broadband providers.
Although this law doesn’t influence PrivateVPN, it may be mandated to materialize users’ data records by the 14-Eyes member states.
But users need not worry as the provider’s only record the email address and password used to sign up for the service. No session data of any kind is collected, including timestamps, server locations, bandwidth, or any other data linked to your activities.
Note that PrivateVPN website add-on use cookies that are stored in your browser to remember your setting preference and gather analytic data such as pages viewed. For this reason, we recommend disabling cookies in your browser to hide your online site-visits.
PrivateVPN has just more than 150 servers located in 60 countries. On the downside, the servers may experience traffic overload resulting in slow connection speeds. On the bright side, however, all these servers are operated and owned by the provider.
As far as data encryption is concerned, PrivateVPN employs the military-grade 256-bit key encryption. Still, users’ data may be compromised since the provider uses third-party payment processors. Thankfully, the provider accepts Bitcoin payment, which is a safer payment method.
Pros
- Respectable no logs policy
- Robust encryption standards
- Easy to install and use
- Owns all the servers in its network
Cons
- Needs more servers
Types of VPN Logs
VPN logs are data that providers keep during the usage of their service. When it comes to privacy, remember the VPN providers can access all of your internet activity.
So, it is a good idea to be mindful of what they record and whether they compromise your privacy in the process. For this reason, it helps to know the various types of logs VPN providers can access and record;
Connection Logs
Also known as diagnostic or usage logs, connection logs are kept by the provider to help in troubleshooting technical issues. They are also used to prevent massive abuse of the network by hackers and spammers.
These logs usually consist of timestamps, device IP address, server IP address, and the amount of data transferred. In some cases, this data is tied to an individual account or collected on an aggregate basis.
The logs are often kept for two weeks, though there are providers who keep them for a month. From a privacy perspective, the less time the data is stored, the safer you are, especially if the logs are collected on an individual basis.
Activity Logs
As the name suggests, activity logs entail a user’s browsing data. These logs are considered the most sensitive of all logs since they hold online activities. They include information such as websites visited, files downloaded, and programs used.
Luckily, only a few VPNs are known to keep these types of logs. What’s unfortunate, the few that do collect, often sell the data to advertisers for target marketing. This practice is common with free VPNs, which is why you should avoid them.
By law, mostly, your ISP is required to record your online activities. Some ISPs keep this data for six months or up to two years.
While ISPs aren’t as malicious as hackers, they may use your data to impose bandwidth caps — the more reason you should use a VPN to protect privacy.
Personal Identifiable Logs
Personal identifiable logs refer to the information users provide when signing up for a VPN service. Details contained in payment processes such as bank transactions and debit cards also make up this logs category.
A provider committed to protecting your privacy shouldn’t prompt you to share such details, whether you’re signing up or paying for the service.
For a reason, users should be given the option to sign up with a disposable email address and pay for the VPN using anonymous payments such as cryptocurrencies and gift cards.
Conclusion
If you are looking for a VPN that doesn’t collect any of your data whatsoever, you probably won’t find one. Providers need users’ data to improve their service.
However, the difference comes in the type of data they record. Ideally, the provider should only record harmless meta-data, such as the amount of data transferred. Such is the case with the VPNs listed above.
Although all of them can be trusted to protect users’ privacy, ExpressVPN checks all the boxes. The provider has a consistent privacy policy that establishes its no-logs claims. In addition to its robust encryption, the VPN’s performance is unrivaled, making it an all-round VPN service.