Browsers are ubiquitous when it comes to accessing the internet from anywhere in the world. How these programs are designed determines the security and privacy of users.
Cybercrime has been on the increase in recent years and incidents of data breaches are more common than ever before. There is a rush from major players to collect personal data by tracking user activity and using it to customize targeted ads.
While the combination of security and privacy would be the ideal preference for most users, some of the leading browsers struggle to achieve this dual convergence. Satisfactory user experience is dependent upon numerous features that not only ensure security and privacy but deliver ease of navigation, speed, compatibility and reliable updates.
Today’s web users are more savvy and expect their browsing experience to be fast and enjoyable. Features such as personalized search results are inevitably important yet tricky when it comes to privacy.
The choice of browsers available for internet users is wide and if you are security conscious, then the detailed reviews below will help you narrow down to a favorable choice that meets your requirements.
In this breakdown we shall look at browsers that perform well in managing security threats and have robust systems of staying up to date.
Why is browser security important?
For a long time Microsoft’s Internet Explorer enjoyed a monopoly in the browser market when it was bundled with the Windows operating system. Today it is Microsoft that is advising users not to make it their default browser because it is no longer supported. Users are being encouraged to use Microsoft Edge, the company’s newest web browser.
One of the reasons that led to the diminishing fortunes of Internet Explorer was its history of security problems. Its features kept lagging far behind its competitors with flaws that exposed various vulnerabilities exploited by hackers. This led to the emergence of other more robust browsers such as Mozilla Firefox, Opera and Google Chrome.
Web browsers collect a lot of information about you every time you visit sites. This information can be accessed by the browser manufacturer or other third parties. The data collected by browsers include:
- The websites you’ve visited
- The device you’re using
- The software running on your device
- Your IP address
- Your location
- The pages you visit on a particular website
- Depending on the settings, the browser can store your credentials such as usernames and passwords.
From above, it is clear that a browser holds a lot of information which if stolen can be used for malicious purposes. To ensure all this data about you is safe, a browser needs to have robust features that protect you every time you go online.
While speed, ease of use and personalized search results may be important, as a browser user you need to look out for two major factors when making a choice of the most secure browser;
- Updates – a secure browser should have regular updates to keep up with new technological developments which are exploited by hackers.
- Features and tools – a browser should have specific security features to protect users from any external attacks. Privacy tools should enable users to decide what to share with manufacturers and advertisers.
While the major players like Chrome, Internet Explorer (and its successor Edge), Safari, Opera and Firefox are popular with users, other little-known browsers like Brave, Chromium, Waterfox, Epic, Comodo Dragon, Tor and others are equally powerful and adept at prioritizing your security and privacy in a more direct way.
Google Chrome
In the web browser ecosystem, Google Chrome is undoubtedly the market leader with a whopping 64% share globally as at the end of 2018. This growth has happened over the last few years and can be attributed to two fundamental features – functionality and security.
While the browser is only ten years old, it has transformed itself into a major player that is responsive to consumer needs. It is functional with an intuitive user interface that is not only uncluttered but has curved shapes.
Great features on Chrome
- Alerts about dangerous websites that launch phishing attempts
- Alerts about downloads that may contain malware
- Enables the search function straight in the address bar
- Updates are installed automatically to patch any security vulnerabilities
- Prevents malware installation through sandboxing
- Saves passwords and has enabled passwordless logins.
Chrome has an Incognito mode which allows you to browse anonymously. This mode simply does not store the history of websites you visit, cookies and related information for that particular session.
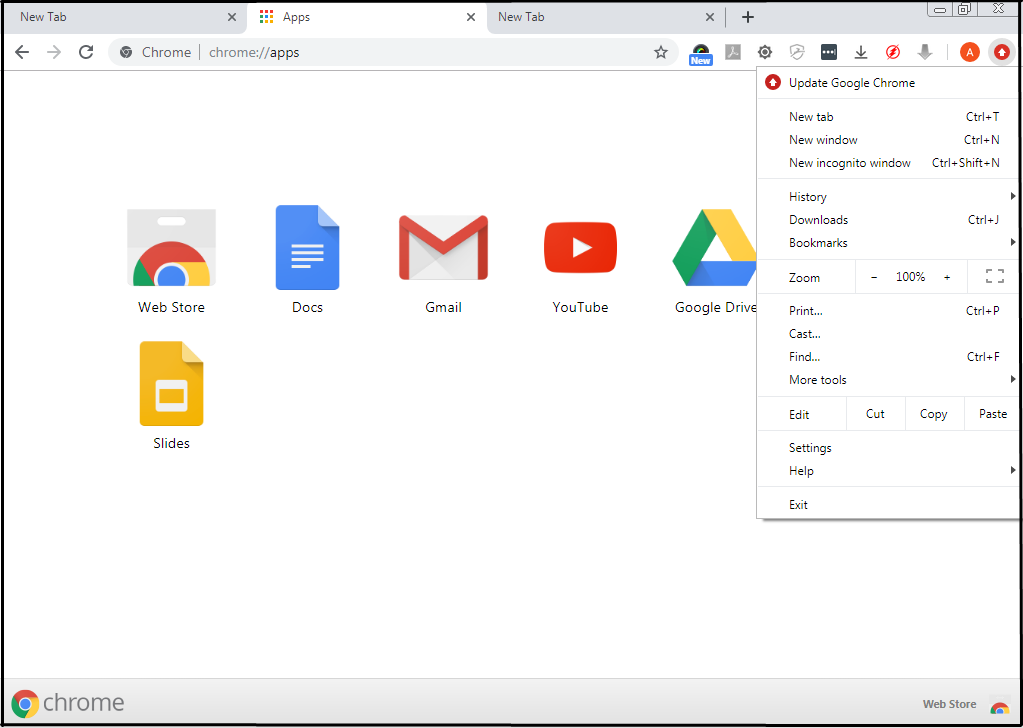
It’s important to note that the Incognito mode does not provide anonymity from surveillance by a government or your ISP and neither does it protect a user from hackers. It simply doesn’t leave a trace of your activities on the browser.
Google has performed well in terms of security compared to other browsers. Ethical hackers at Pwn2Own browser hacking event have on several occasions breached other browsers like Microsoft Edge and Firefox but found an impenetrable fortress at Google Chrome.
The scanning of downloads protects users from installing malware on their systems and the anti-phishing blacklist warns users when they attempt to access potentially harmful websites. Chrome users are therefore robustly protected every time they are online.
Within the tabs on Chrome, sandboxing prevents interaction with the operating system, safeguarding the system from requests that do not originate from the user. This protects user files and other important areas like the operating system memory.
One weakness with Chrome is the lack of a master password to protect passwords stored by the browser. Users may choose not to store their credentials and instead use a password manager.
Chrome is a product of the search giant Google. Users keen on privacy may find this browser sneaky in the way Google tracks their online activities to understand behavior and build a profile that enables the company to offer targeted ads.
While such characteristic tracking can help improve user experience by for example, making useful suggestions during web searches, it may be considered as an intrusion into a user’s privacy,
Microsoft Edge
Microsoft Edge is the newest browser from the tech giant that is bundled as the default browser on Windows 10. Edge is actually supposed to completely replace Internet Explorer at some point. At the moment Microsoft is only offering limited support for Internet Explorer 11.
After many years of vulnerabilities in Internet Explorer, Microsoft has finally produced a browser that seems to play in the same league with the big names like Chrome and Firefox.

The browser is based on the open source code for Chromium but with superior features compared to Chrome.
The browser’s Windows Defender SmartScreen technology is critical in detecting and preventing phishing sites that steal sensitive user information. This feature also detects and blocks malware more robustly compared to Google’s Chrome and Mozilla Firefox.
Another outstanding feature is the sandboxing technique which isolates running programs to thwart any attempt at exploiting software vulnerabilities while the password management feature helps to secure sensitive data within the browser.
Some phishing sites have gone a notch higher by deploying encryption. Microsoft Edge has been found to be effective in identifying such sites which steal user data.
Using the Windows Update service, Edge allows users to receive automatic updates that help to secure the browser against any emerging threats. Any vulnerabilities are addressed through such security patches that happen regularly.
Windows 10 users are encouraged not to disable automatic updates to the operating system. Disabling these updates may result in a missed opportunity to patch a security vulnerability which is likely to compromise browser security.
Microsoft Edge has a “Do Not Track” feature which can be used to prevent websites from tracking your activity while online. However, it has been noted that this feature is ignored by most websites.
The browser has the “InPrivate browsing” mode which enables users to browse without storing cookies, temporary files or the browsing history.
Microsoft does not serve targeted ads on Edge but the company, just like Google, is known to track user activities and collect data for other marketing purposes.
The level of privacy for this browser may not be satisfactory but it scores well in terms of security.
Opera
Opera is a Chromium-based browser that has marketed itself as a lightweight program that enables users to achieve greater privacy. Several features stand out for this browser.
It includes a built-in ad blocker which is effective against pop-up ads. This feature requires enabling via the “Settings” menu since it is disabled by default.
Opera has put user privacy on the forefront of its basic features by including a built-in VPN (virtual private network). The VPN routes browser traffic through different servers around the world to disguise your IP address and location. The data transferred through the VPN is encrypted to prevent anyone from accessing it.
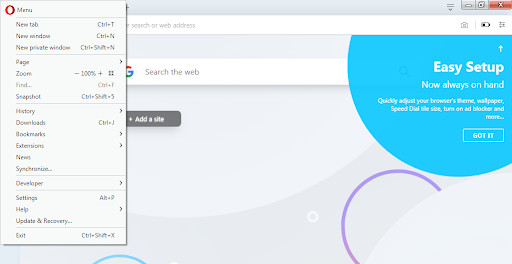
A VPN protects user data and ensures complete anonymity of online activities. The VPN feature, although limited with only 5 server locations, is an attractive addition to this browser and was made possible after SurfEasy”s acquisition of Opera in 2015.
Opera offers a Security badge service which provides information about the webpage visited. The browser also detects and blocks phishing sites and protects against malware attacks.
Opera comes out as a strong contender for browsers with an emphasis on privacy but it collects some information about users for sharing with trusted third parties.
Epic Privacy Browser
Another Chromium-based browser is Epic Privacy Browser. It is based on Google’s open source code but has distinguished itself as independent of any Google services. This browser has enabled the “Do Not Track feature” by default and operates in private browsing mode at all times – deleting all trackers, cookies and other search-related data after each browsing session. Google cannot track your user activity on Epic unless you browse the web while logged in to Google services.
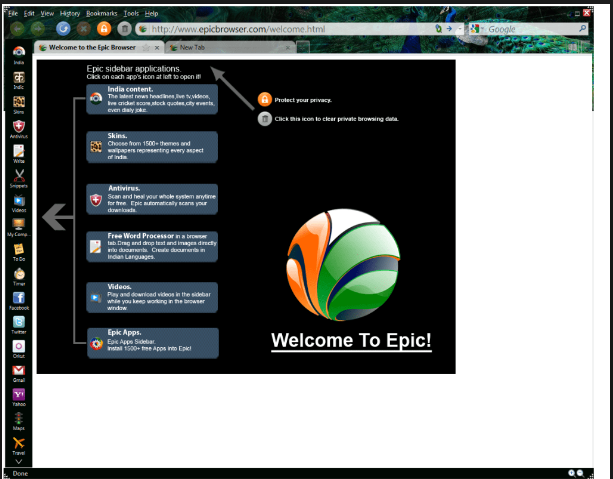
Epic is capable of protecting your online privacy by hiding your IP address through the use of a proxy server. This encrypts your connection and ensures that any sensitive information is secure.
This browser is programmed to use SSL connections whenever available to ensure all connections are secure, especially for those using public wifi. The built-in ad-blocker is an important addition which helps users avoid annoying ads.
Users may find the lack of support for addons disappointing but Epic cites extensions as risky features that can easily compromise user privacy hence it allows only a handful of trusted addons.
The browser prides itself for not collecting user information but only identifying IP addresses for location-based search results.
Mozilla Firefox
Mozilla Firefox has been a leader in the browser arena for a while before it was upended by Google Chrome. This happened in the past three years when updates to Firefox took longer to catch up with emerging trends.
With improved security and privacy features this browser continues to be a prime example of resilience in the face of increased competition.
Some of the features in the latest release have improved responsiveness while maintaining privacy and security. Key among the features are:
- The browser utilizes Linux Sandboxing to protect users against hackers.
- Add-ons and other features are recommended based on browsing behavior of users. This is referred to as the Contextual Feature Recommender.
- The Enhanced Tracking Protection is a feature that blocks any tracking attempts from websites while Firefox Monitor warns users if their email is used in any attack.
- The Control Center gives users greater control by allowing them to customize settings for a private and secure browsing experience.
The Firefox browser benefits from regular updates which have enabled it to stay ahead of competitors in terms of security and plugging any vulnerabilities that may be used by attackers. The browser has been strengthened to detect spoofing attacks and with the Tor add-on, users can increase their privacy to unprecedented levels.
Comodo Dragon
Comodo Dragon is similarly based on the Chromium open source code. Although it has taken up most of the features found on Chrome, it emphasizes on privacy while adding some elements of security that users may find useful.

Its limitation to the Windows platform (Windows 8, 7, Vista, and XP) may be a disappointment to some users but it supports various add-ons which improve user experience by adding the much needed functionality. A few features stand out for Comodo Dragon. These include:
- The ability to detect and block tracking and all cookies
- Technology that identifies secure SSL certificates necessary to validate domains.
TOR
TOR or The Onion Router is a browser based on Mozilla Firefox. It is unique because it uses a network of volunteer servers around the world to hide your IP address for anonymity and encrypt your connection to protect your data from prying eyes.
This browser has gained popularity among human rights activists and journalists as a way of avoiding surveillance from state actors. This shows how secure this browser is since it channels your traffic through a network of virtual tunnels which are run by volunteers all around the world.
Tor is a free, open-source software that is available for anyone to download. After installing the browser you can attain a great level of anonymity to browse the web without being tracked by anyone.
This browser anonymizes web traffic by encrypting the connection and routing it around the internet through a series of relays spread out across the world. The network is able to conceal your location and activities from any surveillance.
The use of encryption ensures that any data sent through the network is safe and cannot be seen by hackers, your ISP or government agencies. Journalists working on sensitive stories and human rights activists in countries with repressive regimes have effectively used the Tor browser to relay information securely.
Although Tor secures data and protects the privacy of users, it is possible for ISPs and other surveillance entities to notice that it is being used.
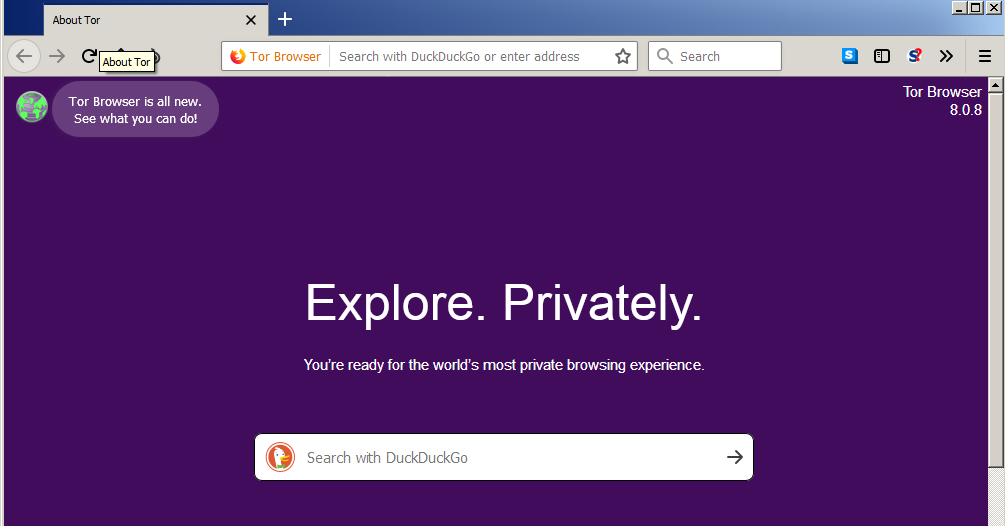
Points to note about Tor:
- Some websites may restrict the use of Tor.
- An ISP or someone monitoring your connection can notice that you are using Tor although they cannot see which sites you are visiting and neither can they see intercept your data.
Tor is one of the most secure browsers and the inclusion of the DuckDuckGo search engine makes it the safest way to search the web.
Safari
The Safari browser is native and available to the MacOS and iOS platforms only. It has some specific privacy and security features which protect users from inherent online threats.
Some of the features include:
- The sandboxing feature can detect malicious code on websites and block any attempts to launch or install malware on user devices.
- The Private browsing feature ensures that information on user activity is not stored or collected by the browser.
- Harmful sites alert is another feature that warns users when they try to access a potentially dangerous site.
- Intelligent tracking prevention is a feature that helps users to prevent cross-site tracking and isolate advertisers.
On the settings menu, Safari allows users to tweak the browser for extra security by disabling location, blocking cookies, disabling Java and requiring websites not to track you.
Chromium
Chromium is the open-source version of Google Chrome. While Google Chrome contains proprietary code that is used to serve Google’s services, Chromium is the bare metal version that is more focused on privacy.
Being the representation of Chrome gives this browser all the benefits of a secure program minus the integration of other code which allows Google to track your online activities and the complexities of third-party apps.
User privacy is guaranteed with Chromium where no data is sent to Google unlike what happens with Chrome.
Chromium uses open-source code which enables users to check for any vulnerabilities and whether they have been patched.
As a Chromium user you need to look out for the following:
- Only download from the official Chromium site to avoid fake programs masquerading as Chromium yet they contain malware.
- Have a regular manual update of the browser to deal with bugs and vulnerabilities. This is helpful because the browser doesn’t update automatically.
- Chromium does not allow you to disable WebRTC. This leaves you vulnerable to WebRTC leaks. If you are concerned about such leaks then you need to use a VPN as an additional measure or use an add-on like WebRTC Leak Prevent.
Brave
The Brave Browser is an open source program based on Chromium. It is available for Windows, MacOS, Linux, Android and iOS. The tracking protection, script blocker and built-in ad-blocker have made this browser lightweight, super fast and functional.
The integration of HTTPS Everywhere and the WebRTC leak protection features have made it the most secure browser among its peers. To ensure you have the latest security fixes, Brave automatically checks for updates.
Privacy for users is improved through the anti-fingerprinting function which blocks fingerprinting scripts.
Regular updates are a key feature of this browser, ensuring that users have the latest security patches. Under the security settings Brave allows you to select what data will be deleted when the app is closed.
With its code based on Chromium, Brave makes it simple for users to continue deploying their Chrome extensions such as LastPass.
Brave features blockchain-based tokens which can be used to reward content creators in a secure transaction while the “Private Tabs with Tor” stops trackers and provides a greater level of protection for you.
In a nutshell the Brave browser delivers the following key features:
- Automatic HTTPS Everywhere for a secure connection
- Blocks fingerprinting scripts
- Does not store your browsing data
- Blocks ads and trackers by default
- Has a built-in script blocker
- Has WebRTC leak protection
With its minimalistic design, Brave delivers fast performance and is a good choice for users with a focus on privacy.
Pale Moon
If you are looking for an older version of the Firefox browser without the features that infringe on your privacy, then Pale Moon would be your choice. This browser supports older add-ons for Firefox and has not moved quickly to embrace newer ones.
Since it uses open-source code based on Firefox 38 ESR, the browser is highly customizable and has all the tracking, telemetry and data collection of Firefox removed.
The key features of Pale Moon are:
- highly customizable, user-friendly interface
- Support for older Firefox add-ons
- Purged of tracking, data collection and Telemetry for improved security
The browser is available on Linux and Windows platforms.
Waterfox
Like Pale Moon, Waterfox is another browser based on the open-source Mozilla Firefox. In the same breath as Pale Moon, it does not track your online activities.
The key features of Waterfox include:
- Support for older Firefox add-ons
- User-friendly interface
- Open-source based on the Firefox browser.
- No tracking, startup profiling, sponsored tiles, data collection and Telemetry
A point of concern for Waterfox browser is the lack of regular security updates.
Iridium

Iridium, just like Brave is also based on the Ungoogled Chromium browser. It is devoid of the code used by Google to track users and feed them with ads.
Its main attractions include:
- Open-source code
- A user-friendly interface
- Enhances security by blocking ads and trackers and not storing your browsing data
- Asks for your permission to transmit queries and keywords.
Additional tools to make your browser secure
In this section we look at some add-ons and extensions you can utilize to improve the security and privacy of your browser. However, it is important not to merely download any add-on to your browser. Some of them have been known to carry vulnerabilities that can compromise the very security you are trying to fix.
Here are some of the best add-ons you can try;
- HTTPS Everywhere – This browser extension forces every website you visit to implement a secure connection using HTTPS (S stands for “secure”) instead of HTTP. This extension is open-source and can be downloaded from the Chrome web store or from here.
- DotVPN – This free extension protects your identity while you’re browsing online. It acts as a VPN proxy for your browser securing your device connection when you’re connected to public wifi hotspots, cellular data networks and other public locations while protecting your identity and foiling censorship.
- Privacy Badger – This add-on automatically blocks invisible trackers. It is good at blocking all kinds of spying advertisements and trackers.
- uMatrix – This is an advanced plugin that requires configuration to execute. It operates like a firewall and allows you to configure what activities the browser can execute for example what type of data the browser is allowed to download.
- NoScript – This extension allows you to customize specific scripts that you would like to run on the websites you visit. It is similar to uMatrix and requires considerable customization to prevent it from breaking all sites by default. You need to have advanced knowledge of what each script does on a website.
- uBlock Origin / Adblock – Just like Privacy Badger, these extensions are able to block any annoying ads and pop-ups. They also effectively block the trackers associated with those ads.
- Ghostery – This add-on gives you total control over trackers by allowing you to decide which ones to block and which ones to allow.
- Cookie Autodelete – This extension automatically deletes any cookies that are no longer used by your browser.
- Click & Clean – This extension clears all traces of your online activity. It is a cleaner that deletes all the cookies stored by your browser and also clears the cache after your browsing session.
- Decentraleyes – This add-on blocks content delivery tracking without breaking the web pages. It prevents a lot of requests from reaching networks like Google Hosted Libraries, and serves local files to keep sites from breaking.
- Avast Online Security – This browser security and web reputation plugin checks every site you visit to ensure nothing puts your device or your data at risk. It provides added security on phishing attacks, data breaches and other cyber-crimes by showing user reviews and warning you if a site is deemed untrustworthy. It autocorrects misspelled URLs to ensure you don’t visit a scamming site and you can easily check the rating of any website by hovering the mouse pointer over the link.
- DuckDuckGo search engine – Unlike the most popular search engines such as Google, Bing or Yahoo, DuckDuckGo is an excellent search engine which does not save your searches nor build a profile based on the activities you conduct online. This helps you to avoid targeted ads that are tailored to your online behavior.
DuckDuckGo does not collect or share any personal information and neither does it store your search history. With no tracking or ad targeting, this search engine gives you the best of Google with added privacy.
This browser extension gives every website you visit a score based on the site’s privacy policies, encryption implementation and any hidden trackers. The Privacy Grade from A to F lets you have a bird’s-eye view of how your personal data is treated and how much a website can be trusted.
DuckDuckGo is available as a browser extension for Chrome, Firefox and Safari. It is also presented as an app for iOS and Android devices.
The Tor browser uses the DuckDuckGo search engine by default.
What else?
Each of the browsers discussed above has its own strengths and weaknesses. Some browsers track your web traffic and use it for targeted advertising. Others sell this information to third parties.
As seen above you may opt to install browser add-ons to improve security but some of them come with risk. Securing your browser may therefore require a combination of different approaches to maximize on what the browser comes with and other options that enhance both security and privacy.
To increase your safety to a comfortable level you need to consider the following:
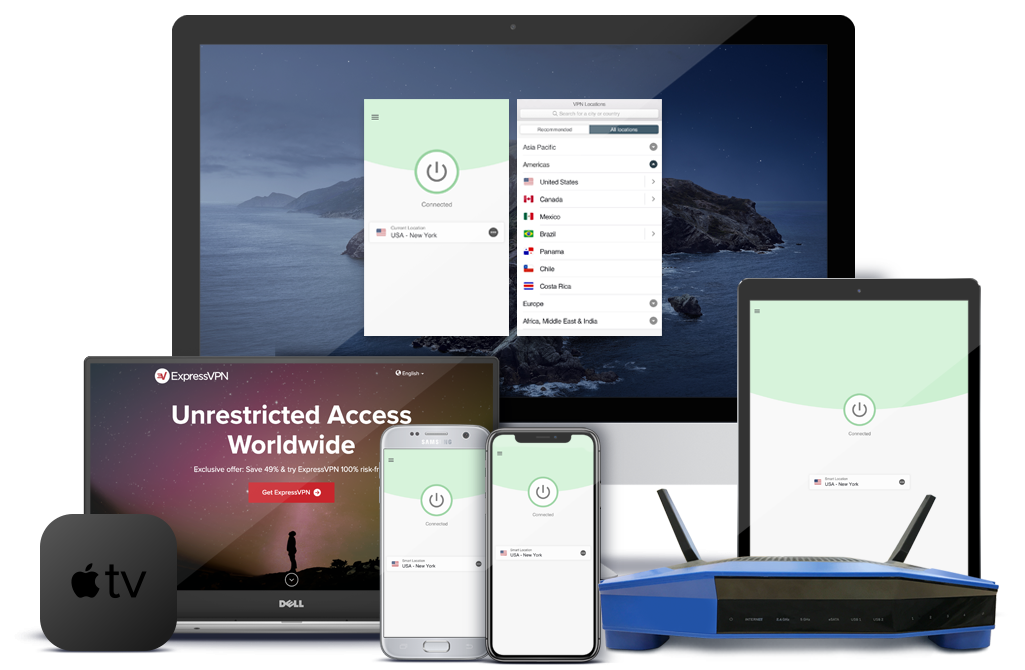
Use a VPN
A VPN or virtual private network is a service that allows you to change your IP address and encrypt data, enabling you to send and receive information securely while remaining anonymous online.
The service basically tricks your device, whether it’s a laptop, desktop computer, tablet or smartphone into thinking it’s in another location. It encrypts all the information that moves to and from your device, increasing your security. Nobody, even your Internet Service Provider can snoop on your communication.
Configure browser security settings
Tailor your browser security settings based on your needs. Every browser has privacy and security settings that can be tweaked to suit your browsing environment and secure your data.
Some browsers will allow you to determine what information can be shared with third parties and you can even disable cookies and trackers. Such a customized security environment is possible if you take time to work on your browser settings.
Use multiple browsers
So many online services like Facebook, Google and other content providers require users to log into accounts to access their sites. This action allows these websites to track your online activities which are directly linked to your identity. This puts your privacy at risk and makes it difficult to surf anonymously.
You can solve this problem by assigning certain browsers for specific activities. For example, you may use one browser that is secure for services that require you to log into accounts and another one for web browsing which you do not want to be tracked.
This method will allow you to avoid being tracked by third parties online as long as you keep to your assigned browser and associated activity.
Use a reputable Antivirus program
While your browser may be among the most secure ones we have seen above, it won’t thwart all cyber threats that come its way. You need to have a robust antivirus program that will prevent malware from infecting your device and can block harmful sites before they load.
If you already have a reputable antivirus program, it is important to ensure that it is updated regularly to keep up with emerging threats.
Use a Password Manager
Some browsers allow you to store usernames and passwords for ease of logging into websites. If the browser has vulnerabilities then your credentials are at risk of being stolen by hackers.
To avoid this, invest in a reputable password manager that will securely store your credentials and help you fill out online forms without remembering your passwords. A password manager is a software application that will store and manage a large number of passwords for you. It stores the passwords in an encrypted format and can only be retrieved by inputting a master password.
Making a choice
While speed, customizability and search functionality are key components on a web browser, security considerations are critical in safeguarding data and other sensitive user information.
You will realize that in our breakdown, some of the bare-metal versions of the popular browsers are secure but tend to prioritize privacy. The challenge of regular updates to these versions is a key consideration when determining how they rate across the board.
Other browsers like Tor use advanced technologies to encrypt data streams on transit and combine this with anonymity as an added advantage.
In our analysis, the following browsers stand out of the crowd with features that make them our top secure browsers of 2019:
- Google Chrome
- Tor
- Firefox
- Microsoft Edge
- Brave
- Epic Privacy Browser
- Chromium
- Opera
The Rundown
As we have seen above, the numerous web browsers on the market offer various levels of security and privacy. Each browser may not be perfect but the combination of features can bring it closer to being the most secure browser.
A browser like Chrome may score poorly on privacy but is strong on security. You can employ other tools such as HTTP Everywhere or VPN to compensate for what your current browser is lacking.
The security of a browser boils down to how effective it can use the inbuilt tools to thwart malware attacks and how fast any bugs and vulnerabilities can be patched through security updates.
Search tools are some of the most ubiquitous elements of a browser and need to provide convenience in addition to being user-friendly. While most browsers offer exceptional protection against malware, others may fall short of expectations while others may give a combination of secure connections and privacy settings that can be tweaked to give you anonymity online.
With all these factors in play, every user looking for the safest web browser must also consider their own preferences in the final analysis. Key considerations will always revolve around security, whether you are comfortable seeing ads in your browser and how much personal information you are willing to share with the browser developers and third-parties involved in targeted advertising.
The most secure browsers must keep abreast of the fast-changing world of technology through regular updates and patches to any identified vulnerabilities to ensure that users are protected. They must also meet your unique needs as a user for ease of navigation and convenience.